[ad_1]
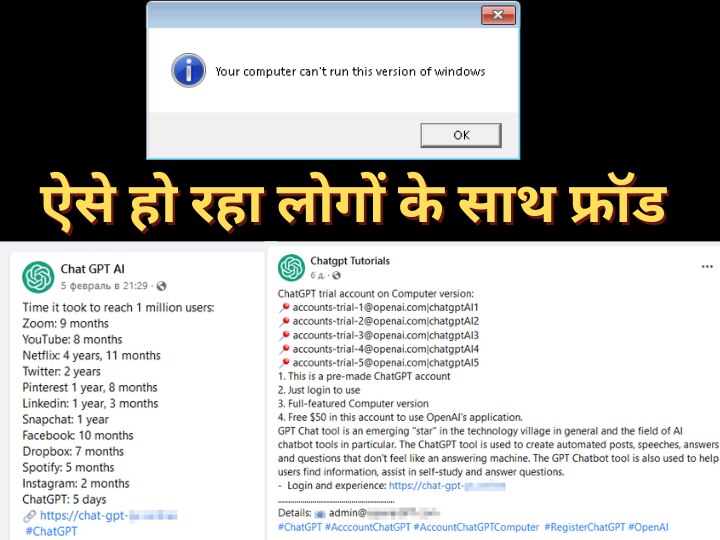
If you use Chat GPT then this news is important for you. Actually, scammers are taking wrong advantage of the popularity of chatbots and are doing fraud with people. Some researchers of cyber security company Kaspersky have discovered a fake desktop app of Chat GPT, from which people’s data is being stolen. The company told that a fake link is being circulated on the social media platform, in which people are being told to get $ 50 for downloading the app. Researchers told that in fact, on downloading the app from this link, a malware comes in the background in the system and then it steals the data of the people.
The game is happening in the background in the name of the app
The company has identified this new malware as Fobo (Trojan-PSW.Win64.Fobo). Researchers told that hackers have created a fake website called Chat GPT which looks exactly like the official website of Open AI. As soon as people download this app by clicking on the link, the process stops in half but actually malware gets installed inside the system. It is from here that this malware steals personal information of people such as Google, Tick Talk, Facebook, Instagram etc. Kaspersky also disclosed that the attackers are targeting the global market as the way the traffic of Chat GPT has been increasing in the last few months, scammers are making it their prime target.
 News Reels
News Reels
Let us tell you, Open AI has not yet created any app or software for Chat GPT. So don’t trust any link or app. Always access Chat GPT only from its official website. Do not trust any link or app coming on social media because it is causing fraud. Scammers are also doing many types of posts to entice people.
this is the official page
This is the official website (https://openai.com/blog/chatgpt/) to access Open AI’s chatbot ‘Chat GPT’. Apart from this, do not trust any other app or link.
Read also: Now ChatGPT will reply to the messages coming on WhatsApp… How? this is the way
[ad_2]
Source link